A enumeração de e-mails é uma técnica utilizada para identificar e validar endereços de e-mail existentes em um domínio específico. Seja para fins de teste de penetração, marketing ou simplesmente por curiosidade, entender como essa técnica funciona é essencial.
Um invasor pode usar os e-mails detectados para procurar senhas vazadas por exemplo, realizar testes de engenharia social ou para realizar testes de força bruta.

Dominios e formato
O primeiro passo para uma boa enumeração é descobrir os dominios do alvo. E a palavra dominios está no plural de forma proposital: Pense que grandes empresas costumam possuir mais de um dominio, as vezes possuem algumas join ventures ou filiais que podem ser alvos e fazem parte da cadeia de ataque, os quais devem ser também enumerados a depender do escopo. Para identificar os dominios a utilização de buscadores como o Google é uma das melhores opções. Exemplo, supondo que o alvo seja uma empresa chamada EmpresaTeste. Ao buscar no Google por este nome, você provavlemente irá se deparar com o site dessa empresa, suponhamos que seja empresateste.com.br. Na grande maioria das vezes o dominio do e-mail é o mesmo do dominio utilizado no site da empresa. O proximo passo é ainda utilizando o proprio Google, seria fazer uma busca pelas strings “email” “empresateste.com.br”.
Provavemente irão aparecer alguns poucos e-mals nesta busca, principalmente e-mails de sac, contato e atendimento. Isso porém já ajuda a entender se estamos no caminho correto e começar a entender o formato de e-mails.
Linkedin Scraping
O LinkedIn scraping envolve o uso de técnicas manuais e/ou ferramentas automatizadas/scripts para extrair dados valiosos, como perfis de usuários, nome e sobrenome e informações de empresas da plataforma LinkedIn. Esses dados extraídos podem ser usados para diversos fins, incluindo geração listas de e-mails.
De forma manual, este scraping pode ser feito indo na busca do Linkedin, procurando pela empresa alvo, no nosso caso é a Empresa Teste

Após acessar o profile da empresa alvo, basta ir na guia “Pessoas”

Ao acessar a guia “Pessoas” você terá acesso a todas as pessoas que se declararam como usuários que trabalham naquela organização. Mais para frente veremos depois como validar estes e-mails. A partir dai, basta montar uma lista com o nome e sobrenome das pessoas que forem obtidas. Vamos supor que a gente obteve os nomes:
- Maria Flor
- João das Coves
- José Brocolis Cenoura
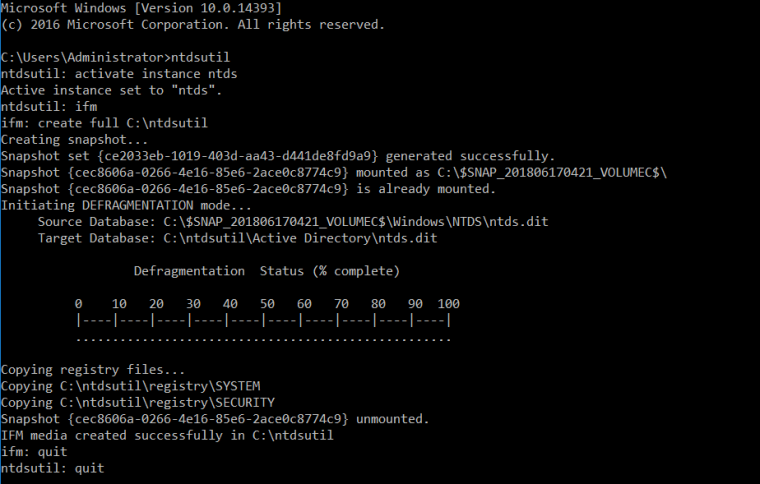
Com esses nomes, pode-se utiliza o Excel,e criar uma planilha com a seguinte estrutura:

Pode-se separar as palavras por espaço
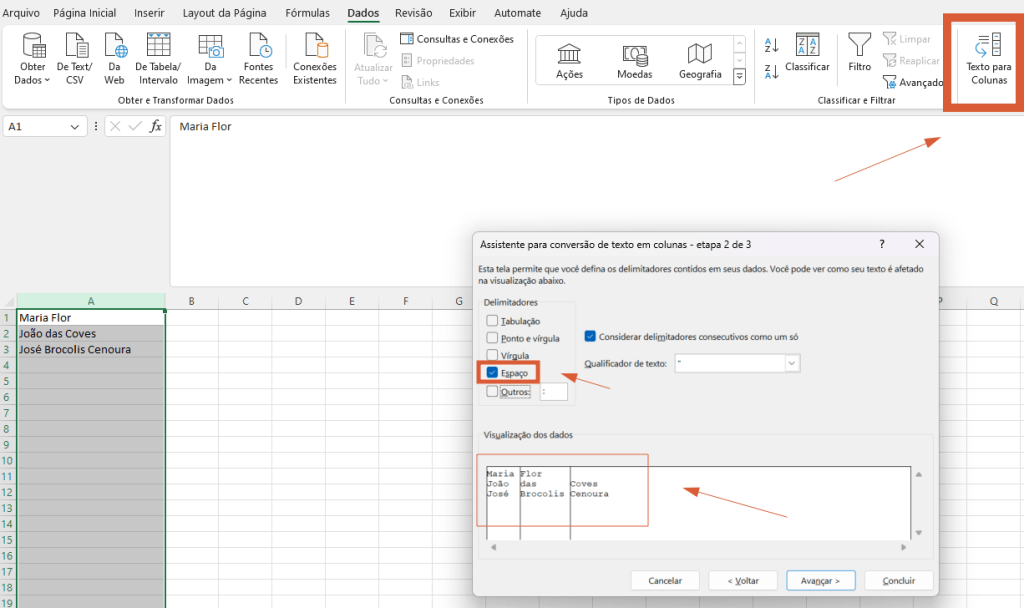
E criar uma lista de possíveis nomes e sobrenomes, caso entenda-se que o formato do e-mail do alvo envolva esses dados Pode-se então criar a planilha com a estrutura: coluna nome, coluna sobrenome, coluna @, coluna dominio e uma coluna concatenando:
Já temos uma lista com 4 possíveis e-mails.
Para retirar a acentuação, pode-se remover manualmente ou usando substituição do excel ou por aqui:
https://www.4devs.com.br/remover_acentos_de_um_texto
Para quem não quiser fazer um processo manual e estiver buscando uma ferramenta que ajude, tem essas duas:
https://phantombuster.com/automations/linkedin/3295/linkedin-company-employees-export
https://chromewebstore.google.com/detail/company-employees-export/lamfphejfohdnnkhfcmhholhkffkeblb
Ferramentas para buscar e-mails
Algumas ferramentas para buscar emails vazados e aumentar consideravelmente a base de e-mails:
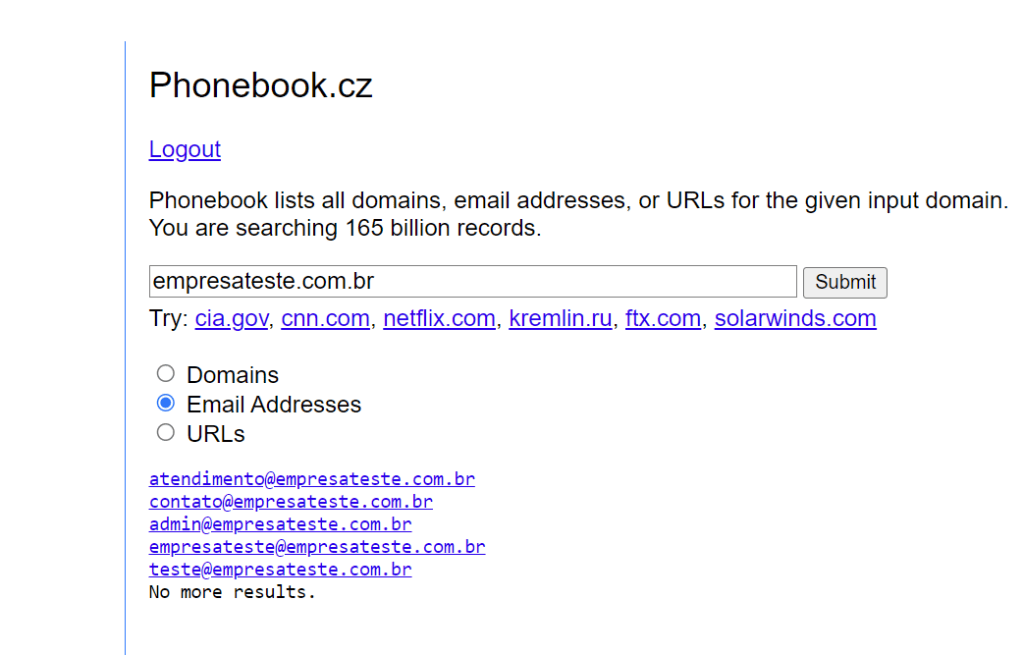
O phonebook é uma ferramenta muito boa e totalmente gratuita. É necessário criar uma conta e estar logado para realizar uma busca. Além de buscar endereços de e-mail, ele também permite buscar URLs e dominios.
O hunter io também é uma boa ferramenta mas o acesso é limitado demais na versão gratuita.

Algumas outras ferramentas que valem a pena serem olhadas:
Validando e-mail
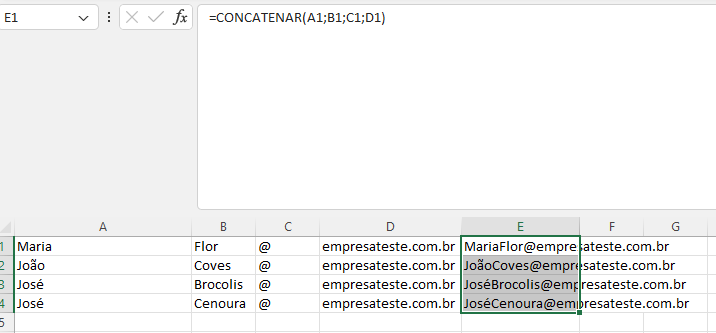
Caso o alvo utilize ambiente Office365, que é um dos mais comuns, existe uma técnica que não gera praticamente logs onde é possível enumerar quais e-mails são válidos. Para isso eu desenvolvi um script para ajudar nesta tarefa que pode ser obtido no meu github:
https://github.com/piffaretti/o365_EmailValidator
Para quem quiser entender o processo por trás do script, a microsoft permite validar e-mails na rota:
https://<tenantname>-my.sharepoint.com/personal/<your user name>/_layouts/15/onedrive.aspx
Se você fizer um curl para essa rota e ele retornar 403, o email existe, se retornar 402 não existe. No lugar do <your user name> é o e-mail que está tentando validar, porém substituindo os pontos e os arrobas por underline, exemplo:
maria.flores@emprestateste.com.br
ficaria neste caso: maria_flores_empresateste_com_br
Outro serviço que pode ser usado para verificar emails e neste caso serve para qualquer provedor é o:
Algumas outras ferramentas interessantes: